
Collaborating to secure our connected world
Digitalization has transformed nearly every aspect of modern life. Today, billions of devices are connected through the Internet of Things. While this creates great opportunities, it harbours even greater risks if we are unprepared.
Founded in 2018 at the Munich Security Conference, the Charter of Trust is a global industry alliance initiated by Siemens because of increasing daily life exposure to malicious cyber-attacks.
Today, its Partners have transformed it into a unique initiative of leading global companies and organizations working together to make the digital world of tomorrow safer.
We envision a world where trust is the cornerstone of global resilience.
In response to the shifting balance of power towards threat actors, we aim to effectively build and embed trust within our alliance and beyond. By fostering strong leadership across the entire value chain, we are uniquely positioned to address global cyber threats, which are exacerbated by emerging technologies such as AI and quantum.
Our vision is to pool our common knowledge and expertise to address these threats collectively, ensuring that trust is the foundation for growing prosperity and advancing society.

Strengthen global cyber resilience through trust by fostering actionable collaboration between industry leaders, governments, and public-private platforms
Our Strategy



Our Approach

We build TRUST
to increase RESILIENCE
through COLLABORATION
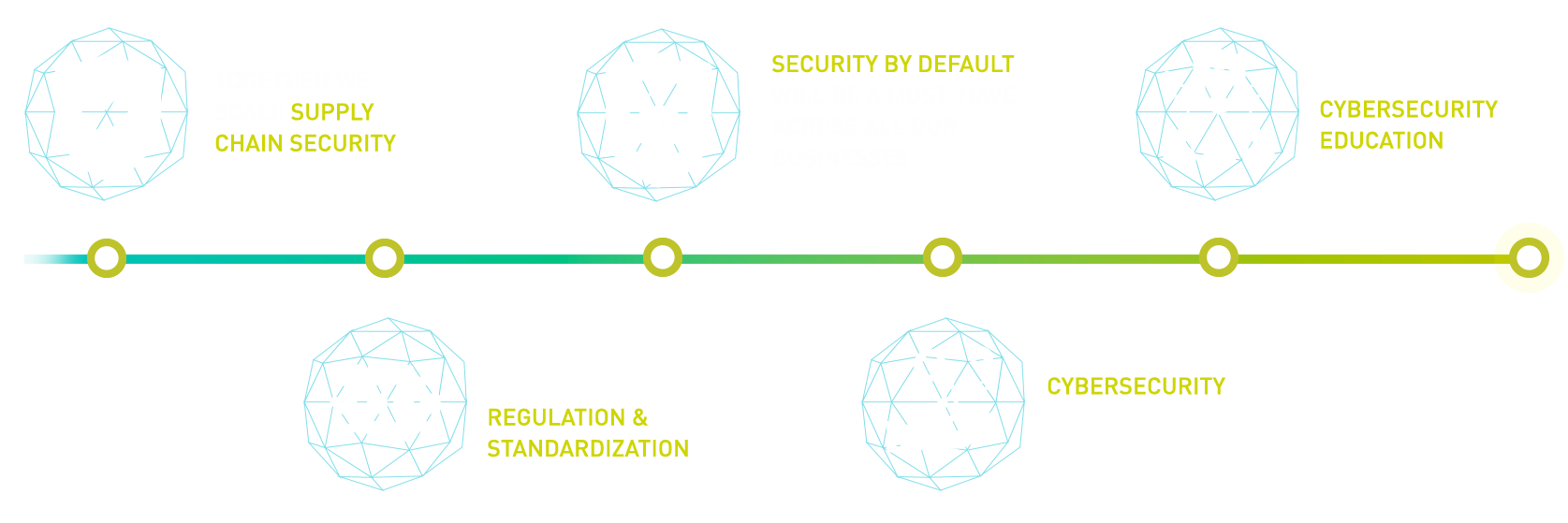
The Charter of Trust is based on 10 key Principles that are fundamental to achieve a secure digital world.
-
Anchor the responsibility for cybersecurity at the highest governmental and business levels by designating specific ministries and CISOs. Establish clear measures and targets as well as the right mindset throughout organizations – “It is everyone’s task”.
-
Companies – and if necessary – governments must establish risk-based rules that ensure adequate protection across all IoT layers with clearly defined and mandatory requirements. Ensure confidentiality, authenticity, integrity, and availability by setting baseline standards, such as
Identity and access management: Connected devices must have secure identities and safeguarding measures that only allow authorized users and devices to use them.
Encryption: Connected devices must ensure confidentiality for data storage and transmission purposes, wherever appropriate.
Continuous protection: Companies must offer updates, upgrades, and patches throughout a reasonable lifecycle for their products, systems, and services via a secure update mechanism.
-
Adopt the highest appropriate level of security and data protection and ensure that it is preconfigured into the design of products, functionalities, processes, technologies, operations, architectures, and business models.
-
Serve as a trusted partner throughout a reasonable lifecycle, providing products, systems, and services as well as guidance based on the customer’s cybersecurity needs, impacts, and risks.
-
Combine domain know-how and deepen a joint understanding between firms and policymakers of cybersecurity requirements and rules in order to continuously innovate and adapt cybersecurity measures to new threats; drive and encourage i.a. contractual Public Private Partnerships.
-
Include dedicated cybersecurity courses in school curricula – as degree courses in universities, professional education, and trainings – in order to lead the transformation of skills and job profiles needed for the future.
-
Companies –and if necessary –governments ensure cyber-resilient products, systems, services and processes through conformity assessments including e.g., verification by independent parties.
-
Maintain and expand a network of experts who share new insights and information on incidents to foster collective cybersecurity; engage with regulators and other stakeholders on threat intelligence sharing policy and exchange best practices.
-
Promote multilateral collaborations in regulation and standardization to set a level playing field matching the global reach of WTO; inclusion of rules for cybersecurity into Free Trade Agreements (FTAs).
-
Drive joint initiatives including all relevant stakeholders in order to implement the above principles in the various parts of the digital world without undue delay.
Our collaboration has shown results.

The Charter of Trust consists of global companies and associated organisations committed to securing the digital world by adhering to our 10 principles.
Together, we shape Cybersecurity.
Our Partners are joining forces to protect our democratic and economic values against cyber and hybrid threats. In this Charter, the signing partners adhere to the key principles we consider essential for establishing a new charter of trust between society, politics, business partners, and customers.
A strong network supporting our mission
The Charter of Trust Associated Partners are regulators, research institutes, universities, and think tanks supporting and promoting the work of the Charter of Trust. Together, we build a trusted network committed to creating a strong digital security environment across the global economy. Our Associated Partners provide valuable insights to the work of our Partners, to assess cyber trends and developments, and to work together on specific Charter of Trust projects.